Cloud Computing Security Defined
by Harikrishna Kundariya,CEO, eSparkBiz
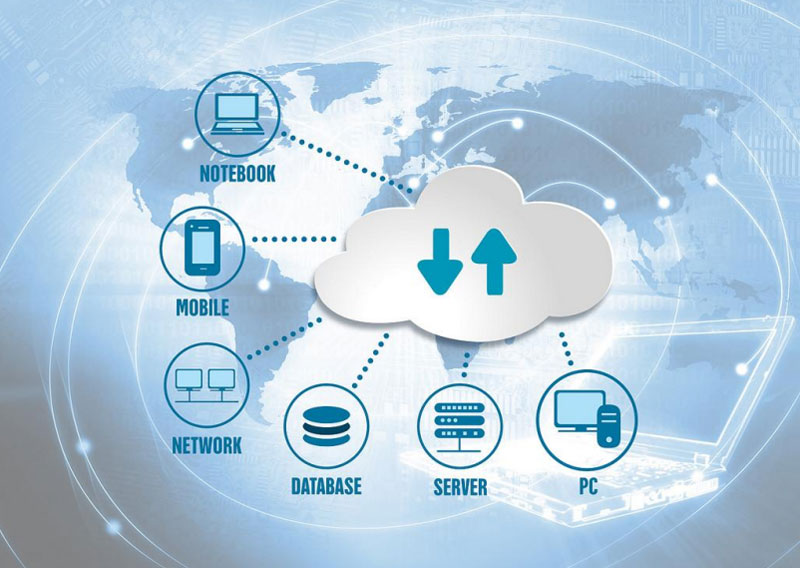
Cloud computing and cybersecurity appear to be diametrically opposed at first appearance. The first option necessitates storing your data off-site, while the second necessitates erecting virtual barriers around it, ensuring that your data is protected at all times. Outsourcing your data and transactions to a vendor is what cloud computing entails. Cybersecurity entails keeping everything close to hand and relying on on-site personnel, processes, and standards to complete the job.
The protection and operation of computer security, applications, data, and information are referred to as cloud security, also known as cloud computing security. Protecting cloud computing against unauthorised access/access, service denial (DDOS) attacks, hackers, viruses, and other threats are part of cloud security. While cloud security refers to cloud computing, cloud-based security refers to security services delivered through software as a service delivery model (SaaS) rather than using on-premises hardware or software. 79% of businesses have had at least one cloud data breach in the last 18 months, with 43% reporting 10 or more breaches in that time.
It is crucial to know exactly where your system can be vulnerable and what you can do about it.
7 Best Practices for Cloud Security
When it comes to cloud security, there are seven best practices to remember.
1. Go with a reputable and safe cloud service provider
When it comes to choosing a cloud service, it is generally best to go with a well-known brand. Choose a cloud service provider with a strong security reputation. Big-name providers have generally had more time and money to improve their security and access control features because they have been in the industry longer.
However, don’t hesitate to rethink your public cloud security model as and when you see fit. You need to make sure you’re covering the essentials and know that it’s a shared responsibility between you and the vendors.
When it comes to selecting a supplier, there are a few crucial factors to consider:
● Response to Security Threats
Have there been any major security breaches at the cloud provider? A fast Google search will usually reveal whether the supplier you are considering has experienced anysecurity breaches or has been the subject of several Denial-of-Service (DoS) attacks. Ifa company has been breached, most organisations respond by strengthening their own and their clients’ security, so do not immediately cross them off your list. Find out more about their security practices by doing some investigation.
● Security Procedures
Is there anything particular in the potential provider’s public policies and/or Service Level Agreements (SLAs) about security and data responsibility? Before committing, if there is no one available publicly, request one.
● Compliance
Is the service provider able to deliver completely compliant servers? PCI, HIPPA, GDPR, CCPA, and SOC all have extremely precise security configuration and practise requirements. Rather than working harder with many cloud hosting providers, consolidate your infrastructure with a single cloud host and work smarter. How can the service providers you are considering meet these requirements? Many companies supply infrastructure that meets these requirements “out of the box.”
2. Recognize your security and compliance obligations
When you first start using a cloud provider, keep in mind that the provider and the end-user share security and compliance responsibilities. You should be clear about where your end-user duties start and stop. Once you know this, you may concentrate your security efforts on the areas where you have authority.
When evaluating security and compliance duties, there are a few factors to keep in mind.
● Cloud Service Provider Policies
A number of policies, such as an Acceptable Use Policy (AUP), Terms of Service (TOS), and Privacy Policy, are likely in place at the service provider. These policies will frequently include important information about the service provider’s perspective on data ownership, security, and responsibility of data that you have as a client, submitted on their platform.
● Data Retrieval
Your company needs to know what data will be stored on the cloud service provider’s platform. For specialised purposes, it is not uncommon to work with many providers. It is vital to maintain track of whether providers’ systems comply with standards for specific data kinds or not. It is vital to understand what types of data you will be storing and how that data will be handled in accordance with rules like GDPR, CCPA, HIPAA, and PCI.
3. Strengthen Access and Security
Before you or your company begins uploading data to the cloud, you should evaluate all security and access settings. Within your organisation, you should have a clear knowledge of who should have access to what types of data. Access to your cloud infrastructure should be restricted to those with enhanced or privileged access. Everyone who interacts with your cloud infrastructure should only have access to the information they need to do their tasks.
Do activate popular security features like multi-factor authentication and role-based access restriction.
Review your access and sharing settings at least once a year to understand who can access and share your cloud data and how.
4. Know Your Cloud Provider’s Data Encryption Policy
It is critical to know how a cloud service handles encryption. In today’s world, sending data without encryption is never a good idea. Rather, it should be SSL-encrypted in transit. This keeps data from being intercepted as it travels between the end-user and the cloud serviceprovider through networks.
It is also a good idea to check if your data is encrypted when it is not in use. This means that the data in the cloud provider’s data centre is encrypted on the storage device. Some forms of regulated data require encryption, which prevents a potential bad actor from viewing the data if they gain physical access to the server where it is stored.
5. Policy and Training Development
It is essential to establish clear regulations for who can use cloud services, how they can use them, and what data can be stored there. To ensure that an end-user does not become the source of a regulatory compliance violation or a data breach, train yourself and your employeeson these policies and security settings. End-users must also be taught the necessity of strong passwords and cross authentication. End-users may be irritated by additional security measures, but if they understand the motivations and justifications for the policies, they are more inclined to comply.
6. Access and Usage Audits
Google Drive is the world’s most commonly used cloud storage service, according to GoodFirms report, Usage & Trends of Personal Cloud Storage, with a staggering 94.44 percent usage. With a whopping 66.2 percent, Dropbox, the best collaborative cloud storage, comes in second.
You should audit your cloud service on a regular basis to see who has used it and what they have been doing. Keep an eye out for unauthorised user access and data sharing, and investigate any inconsistencies immediately.
While developing the finest cloud infrastructure security strategy is a good start, you should not think your cloud presence is your weakest link. Take the time to inventory and assess the potential damage that a malicious insider could cause. Take advantage of the chance to establish policies that hold individuals with access to information accountable. Set up a policy of least access and control, and regularly audit permissions and access to your critical data.
7. Address Security Concerns
When it comes to cybersecurity, it is not a question of if, but when. Planning for this situation is the most critical thing you can do. It makes no difference if your data or your cloud hosting provider has been hacked. You should be aware of your risk and have a strategy in place to deal with it. The best time to start planning for security is when you move to the cloud. Access, compliance and security should be a core part of any cloud migration plan.
If you didn’t, the second best time is now.
Further, make a disaster recovery strategy that covers both your infrastructure and your provider in the event of a data breach. When a breach happens, make sure you understand your compliance obligations and respond appropriately.
Conclusion:
As technology advances, our reliance on the cloud will only grow stronger. As these systems get more complicated, there are several potentials security missteps. If you follow these cloud security best practices, you should be able to prevent a few typical blunders.
About the Author
Harikrishna Kundariya, a marketer, developer, IoT, ChatBot & Blockchain savvy, designer, co-founder, Director of eSparkBiz Technologies @SaaS Application Development Company. His 10+ experience enables him to provide digital solutions to new start-ups based on IoT and ChatBot.
Website: https://www.esparkinfo.com/
Twitter: https://twitter.com/esparkbiz


