Business continuity planning (BCP) is the process involved in creating a system that prevents potential threats to a company, and also aids in its recovery.
This plan outlines how an organization’s assets and personnel can be protected during the current COVID-19 crisis, and how an organization can function normally throughout the crisis.
This business continuity plan includes contingencies for human resources, assets, business processes, and any other aspects that could be affected by downtime or failure.
Common Threats to Production
One of the most common threats on industrial organizations is a breakdown of production equipment. That is why manufacturers invest heavily in human capital, hiring skilled engineers and other specialists who can rapidly make repairs when needed.
However, manufacturers should be investing just as wisely in protection against other threats that are just as destructive: Malware, viral diseases, natural disasters, fire & smoke, flooding, utility outages and IT disruptions.
In addition, during the COVID-19 crisis, there’s a lot more remote work and more things are done quickly, rather than with long term planning. This can create security and operational risks. You need to make sure that your remote work connections are secure.
You Need to be in Control
You need to know about all remote sessions, what your industrial workers are doing, and how your facilities are functioning. Also, since you cannot send people physically on site due to quarantines, or there’s limited availability of personnel, you need to do things remotely and they must be automated. If your organization has limited personnel, or budget constraints you might wanted to consider OT cyber security as a managed service.
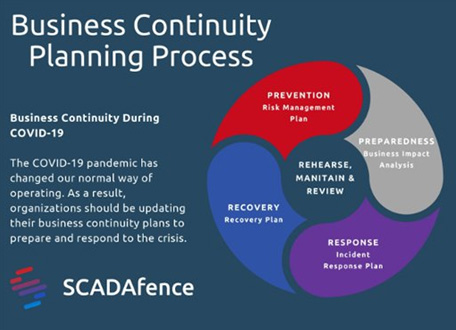
Business Continuity Planning
Below are the key areas that comes into play in ensuring your company’s business and production continuity.
Prevention: Understanding Your Risks
Continuous assessment and visualizations of the risks to your OT network is an essential part of your organization’s preparedness to transition into business continuity (BC) mode.
YouCan Understand Your Risks By:
- Identifying key/critical assets.
- Assessing the risks to your crown jewels.
- Continuous dependencies visibility and a snapshot of your network.
- Ensuring backups and remote access security.
- Ensuring that all employees could sustain production.
- Getting visibility using network maps, remote access and user activity tracking.
Early Detection of Attacks & Vulnerabilities
Over the last few years, the manufacturing industry was hit hard by ransomware attacks. Leading organizations such as Boeing, Nissan, Mondelez and Renault, are just a few of the high-profile producers that have been derailed by infections. Early detection of malware, can significantly lower (and prevent) the impact of a cyber-attack.
Your Organization Can Detect Attacks With:
- Exposure analysis.
- CVE management.
- Centralizedgovernance& compliance.
- Insecure protocols & access.
- Real-time malware detection.
- Continuous reduction of the attack surface.
Preparedness: Asset Management & Identification of Critical Assets
During the prevention and preparedness stages, continuously mapping your assets and identifying the critical assets in your production process is the key to securing them. However, possibly more important during the response and recovery stages, is to quickly identify missing critical assets or inconsistencies in the network’s design and performance. In addition, the ability to compare between primary and secondary sites (as part of responding to a crisis) is crucial.
Your Organizations Can Manage Assets By:
- Maintaining a detailed and updated asset inventory at all times – both in primary and in disaster recovery (DR) sites.
- Managing OT assets down to the model and firmware level, and tracking asset status, owner and location.
- Identifying key/critical assets.
- Creating check points of asset inventory statuses.
- Alerting on any deviation from the asset inventory – including missing, new and malfunctioning devices.
Response: Incident Response
Early detection and rapid response based on predefined playbooks are key to responding to business continuity incidents.
An OT security like SCADAfence, for example,can help your organization by covering both your operational and security aspects. They can provide early detection of potential production interruptions, and ensure continuous production work.This includes remote access, user activity tracking, and permitting access to your 3rd party vendors and supply chain, all without the additional risks of increased attack vectors.
Your Organization Can Respond to Incidents By:
- Detecting and alerting on cyber security and operational incidents.
- Overseeing DR sites operations – and compare them to the approved production status.
- Asset management of your primary and secondary sites.
- Multi-site management.
- Integrating with your existing SIEM SoC systems.
- Full-fledged ticketing and a workflow of current issues.
Recovery: Recovery Mode
After the COVID-19 situation (or any other crisis for the matter) is over and business is returning to normal operations, companies should strive to return to business as usual as quickly as possible. Having an understanding of what business “looked” like before the crisis, tremendously helps in getting back to business as usual. This includes risk assessment reports and compliance reports to ensure that the production system is up and running correctly and is compliant with the industry and the organization’s standards.
Your Organizations Can Recover By:
- Recording “approved” asset inventory status & network state for confirmation of “return-to-normal” state.
- Network traffic activity dashboards.
- Security & network risk assessment reports to make sure the network is secure.
- Standard and policy compliance reports
About the Author
Written by Michael Yehoshua, Vice President of Global Marketing at SCADAfence. Michael brings marketing creativity and out-of-the-box thinking to SCADAfence. Before joining the team, Michael helped turning a small, declining startup into a successful, profitable, world-leading vendor in their vertical leading them to an $18 million Round C investment. Michael studied at Harvard Business School, at Bar Ilan University for his MBA & Lander College for his BS degrees in Marketing and Business Management.


