How a Global Pandemic changed… Everything.
by Anthony Cardoza, Business Unit Director for the Americas, XTN Cognitive Security®

In 1993, the Wu-Tang Clan released their hit song C.R.E.A.M. (Cash Rules Everything Around Me). Although the song was never intended as a model for legitimate businesses to use, the sentiment was held in high regard for the last nearly 30 years. All that has changed in the last few months. In the Old World, it was not unusual to find businesses who only accepted cash payments, like take-out restaurants quietly offering a discount for cash payments, or corner stores discreetly requiring a minimum purchase amount for electronic payment, against the guidance of their point-of-sale system providers (oftentimes pointing you to an ATM located in the back corner of the store). I don’t mean any disrespect to RZA, GZA or the Ghostface Killah (or any of their esteemed colleagues), but I think it is safe to say that C.R.E.A.M is no longer applicable in the world of legitimate business.
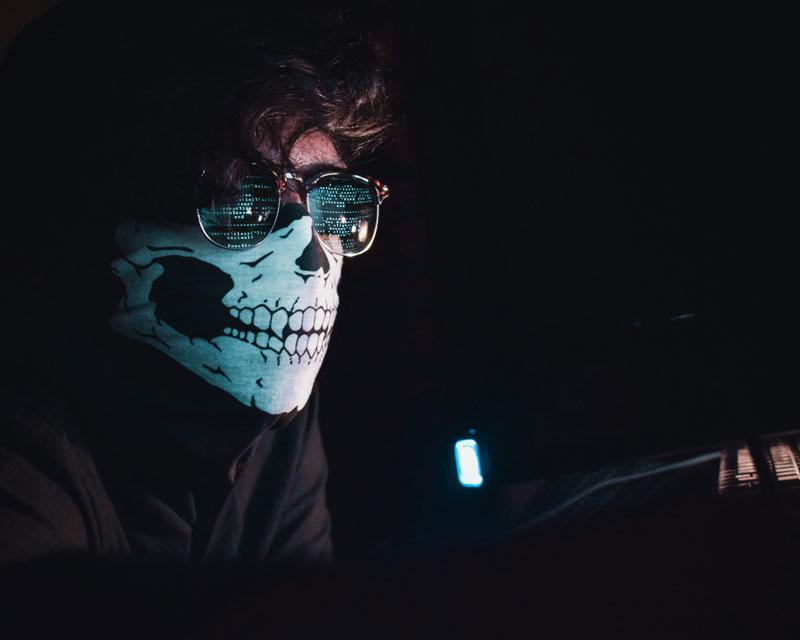
In the New World, cash is considered filthy and it is capable of transmitting disease. Person to Person payments have taken over as the preferred, contactless method for making personal payments. Other options like “Contactless” point-of-sale systems are also experiencing increased desirability, even from “Gen X” and the “Boomers” who had been reluctant to use these types of systems in the past. We are also seeing an exponential increase in the number of IoT devices, like your Smart Speakers, that are capable of placing orders with your favorite online retailers. These new and resurgent trends mitigate against the risk of disease transfer, but also open up new threats and vulnerabilities, leaving hackers, fraudsters, and outright criminals licking their proverbial chops.
In the United States, our ‘paper’ currency is composed of a durable combination of Cotton and Linen, providing ample surface area on both sides for bacteria to reside. Canada, Mexico, New Zealand, and a few other countries have introduced Polymer-based banknotes, which recent studies have shown to carry fewer bacteria. Traditional Point of Sale systems, found in grocery stores, gas stations, and retail shops across the globe, require user interaction with a keypad or touchscreen. These machines can be difficult to disinfect, and usually, they are used by the next customer within moments of the previous transaction. As a result of the changing public sentiment and behavior, there has been an increased demand for vendors to accept mobile payments using newer ‘contactless’ readers. The change in typical behavior is increasing the number of digital payments being made, replacing transactions that had been performed previously in cash. Alongside this, naturally, is an increase in the number of vendors who are accepting these new payment methods. This exponentially expanded attack surface, complete with new/untrained administrators, represents a massive area of opportunity for attackers.
As with many problems, we’ve seen technological solutions implemented and working well. My Barber, unable to conduct business from his brick-and-mortar location, has been making house-calls. And he’s accepting payments through all of the popular P2P payment providers. Our Parent Teachers Association, once a stalwart of the “Make Checks Payable To” era, is now signing e-mail correspondence with their various P2P platform usernames. Even my local 9-hole golf course, which up until this year didn’t accept reservations and preferred cash, now must be reserved and paid for (with a credit card payment over the phone) two days in advance. Needless to say, exchanging credit card information over the phone isn’t the most secure or most convenient way for the customer. Many other area courses have partnered with one of several vendors who’ve made scheduling and paying for tee times available through a mobile application (charging a fee to the course and not the player). It’s clear that the global health crisis has accelerated all of these examples, and it appears that the technological solutions deployed have mitigated the risk of spreading disease and created new opportunities for threat actors.
What other risks do these digital transformations fail to anticipate? What could go wrong with a small Bluetooth enabled device having access to your credit card information, and having the capacity to ‘shop’ online? Worse than your 6-year-old going on a voice-activated shopping spree while you’re in the shower, imagine the scenario where your home network is compromised, and now your Smart Refrigerator is using your credit card to send provisions to Romania. Today, fraudsters have more options for “cashing out” in the real world (thanks to the massive growth of new Payment Service Providers such as Fintech, P2P Payments, and Cryptocurrencies networks). Especially with millions of people in US now unemployed or underemployed, more and more people are willing to participate in cash-out schemes. For example, traditional “forwarding” schemes, where the Fraudster enlists someone to receive a payment, keep a small percentage of the amount, and send the remainder elsewhere, making the fraud much more difficult to track. In the old world, brick-and-mortar vendors kept a special marker at their register to use to detect counterfeit bills. A 5-pack of these pens is available today for less than 10 dollars, including Next-Day delivery. These pens offer no value against digital payment fraud and will be soon be relegated to the junk drawer. New solutions are needed to mitigate the risk of digital payment fraud, without adding complexity, and without disrupting the coveted end-user experience.
Fortunately for businesses going through this rapid transformation, the fraud-deterring technology they need is already available on the market: Our smart devices contain sensors, capable of collecting digital indicators of our identity. Behavioral Biometric solutions can provide strong assurance of a users’ identity without a complicated login process, keeping the sensitive data local to your device, and sending a signal to the Service Provider to be confident in the authenticity of the user. Machine Learning can support an analyst to quickly determine if a users’ actions are human-like or bot-like. Even if the behavior is human-like, it’s critical to understand if the user is legitimate, or if a “Money Mule” account is taking the activity. ML supported transaction monitoring can rapidly detect unusual behavior, human or otherwise, intercepting the transaction to save both the Vendor and the User from the heartache of Fraud Loss, or stopping the money laundering scheme in its tracks. Since all businesses are quickly becoming digital businesses, they’ll be faced with new technological-based threats, and should respond by deploying technological solutions to protect their customers and their business.
If you’re struggling to cut through the complexity of digital payments and need to find a quick and effective way to protect your business and your customers, consider contacting XTN to learn more about our Cognitive Security Platform®. We’ve been helping companies to Trust their Digital User since 2014, and we’re available to help you, too!
About the Author
Anthony Cardoza is XTN Cognitive Security’s Business Unit Director for the Americas, helping organizations to take a proactive approach in the fight against Fraud.
Before starting with XTN in May of 2019, Anthony worked at RSA Security for 6 years, and had previously co-owned and operated a boutique debt collection firm, Boston Enforcement. After nearly a decade driving business results for enterprises and increasing cashflow for clients, Anthony is now focused on empowering businesses to better manage fraud risk without disrupting the customer experience.
Outside of the business world, Anthony is a lifelong musician, and has recently developed a love for growing vegetables. Anthony lives in Danvers, Massachusetts with his wife Alexandra, and their three children Aibhlinn, Austin and Ainsley.
Anthony can be reached via e-mail at [email protected] For more information, please visit our website: www.xtn-lab.com


