by Jalasutram Sai Praveen Kumar, Cyber Security Researcher & Individual Contributor
COVID19 coronavirus pandemic outbreak in early 2020 has significantly impacted multiple countries and diverse industries across the globe. In order to tackle the pandemic, governments across many countries had imposed mandatory lockdowns which in turn forced the businesses to continue their operations remotely. Due to this unprecedented enforcement of remote operations, cyber security blue teams being the watchdog of the businesses, are now facing new challenges in dealing with the situation.
Increase in Phishing Attacks
Capitalizing the panic and crisis situation to their advantage, cyber threat actors became more aggressive in attacking businesses by their COVID19 themed spear-phishing campaigns. Following are some of the phishing attacks themed to COVID19.
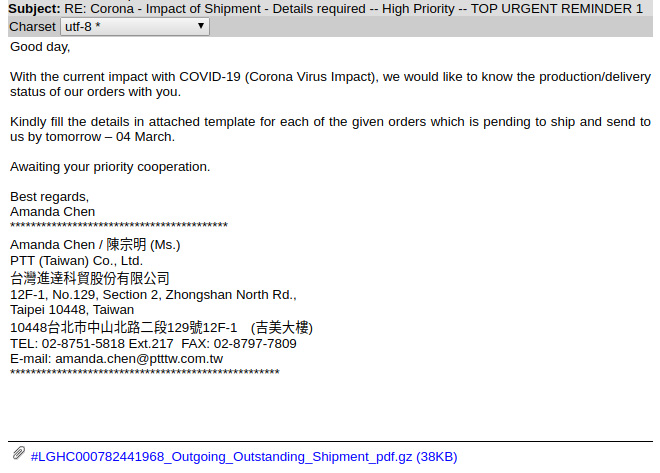
Figure 1: COVID19 Phishing email with a malware attachment
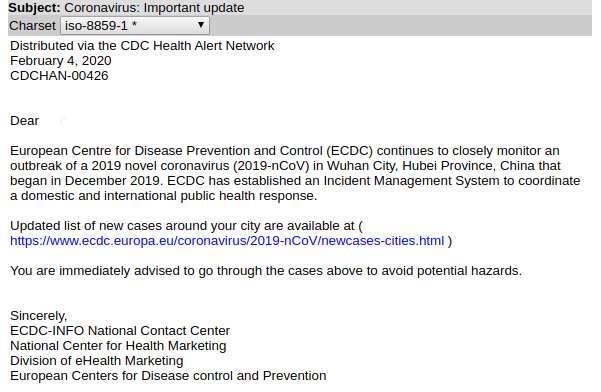
Figure 2: COVID19 Phishing email with a malicious URL
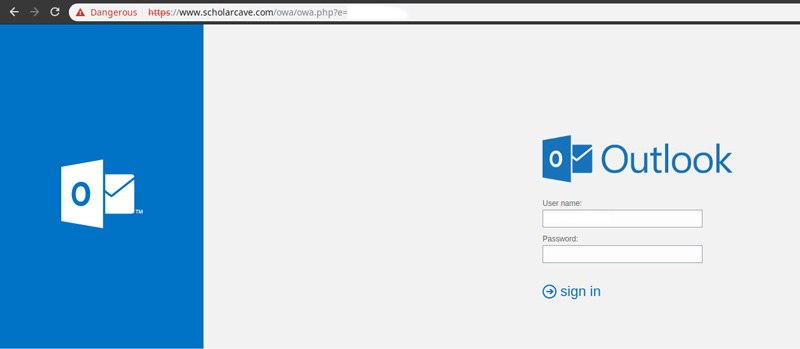
Figure 3: Malicious URL redirecting to Fake Outlook login page
According to a report published by Barracuda Networks, it was observed that there is a huge upsurge in the phishing attacks related to coronavirus COVID19 during the month of March 2020. According to the report, between March 1 and March 23, Barracuda Sentinel has detected 467,825 spear-phishing email attacks, and 9,116 of those detections were related to COVID-19, representing about 2 percent of attacks. Although the overall number of these attacks is still low compared to other threats, the threat is growing quickly and in order to deal with such attacks, blue teams are bound to dedicate resources specifically to handle COVID19 related incidents.
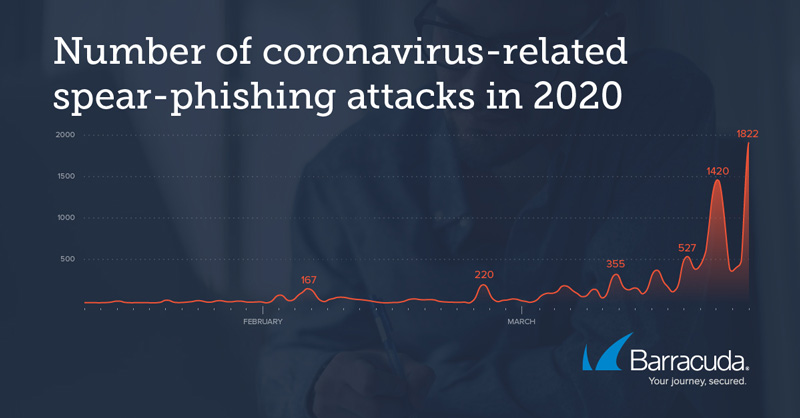
Figure 4: Upsurge in Phishing Attacks for the Months January to March observed by Barracuda Sentinel
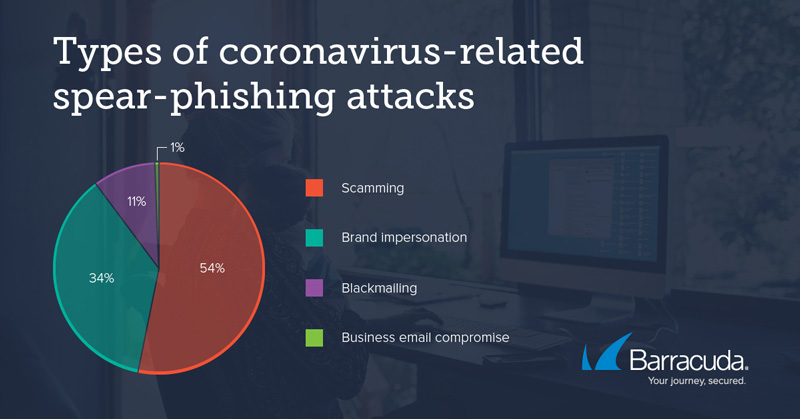
Figure 5: Types of COVID19 Phishing Attacks observed by Barracuda Sentinel
Readiness of Blue Teams for Remote Operations
Blue teams, in general, deal with most confidential data of the organization and operate 24×7 by leveraging various advanced security infrastructure like SIEM, EDR, IPS, WAF, etc. Hence, blue teams traditionally operate in-house and the scope of remote operations for blue teams is considerably low. Considering the unique global situation created by COVID19 pandemic, blue teams are bound to operate remotely and the readiness of blue teams for such rapid switching from in-house to remote operations is a key challenge. In order to ensure 24×7 remote operations, blue teams must ensure appropriate infrastructure and manage appropriate shift timelines to meet the needs. Also, the 24×7 availability of key security establishments and tools for incident triaging and response activities is a key challenge for blue teams.

Figure 6: Readiness Challenges for Blue Teams during Remote Operations
Increased VPN demand and hurried Security Configurations Leading to Increased Risk
Businesses traditionally allow some particular sections of their organizations to operate remotely as normal business operations, however due to COVID19 pandemic, large numbers of organizational employees are embraced to operate remotely using technologies such as VPN and in such situations monitoring the alerts related to VPN security becomes paramount priority for blue teams. Deploying additional VPN servers to meet the demand of the hour and instant configuration of the VPN security controls is a common scenario observed in many large enterprises during these pandemic days. In such cases, any inappropriate misconfiguration of VPN security controls, authentication controls, patching, etc. can lead to a larger risk to the business and such misconfigurations can trigger large number of false positive or true negative alerts. For example, during these pandemic times, creating and deploying possible use cases and playbooks related to VPN activities becomes crucial for blue teams to monitor and triage VPN alerts and activities. Any improper configuration or improper creation of use cases can lead to large false-positive alerts impacting the SLAs of the blue team engagements and leading to larger security risk for the organization.
Increased Efforts in Employee Awareness Programs and Phishing Attack Drills
When it comes to cyber security, employees are the key vulnerabilities of any organization and they are the easy targets for any threat actor performing spear-phishing attacks. Due to the increased chaos and panic related to COVID19 pandemic globally, humans tend to be anxious and excited about any news or articles related to the situation. Levering this to their advantage, threat actors perform spear-phishing attacks using luring keywords such as “COVID19 Symptoms”, “COVID19 Treatment and Cure”, etc. to trap the employees and making the employees aware is another key challenge to the blue teams. In order to avoid employees falling prey to such phishing attacks, blue teams need to employ additional employee awareness programs related to COVID19 and as a part of these employee awareness programs, blue teams also need to increase phishing attack drills.
About the Author
Jalasutram Sai Praveen Kumar is a CTIA, CEH and CND certified cyber security professional with expertise in Threat Intelligence, Threat Hunting, Malware Analysis and SOC engagements. Prior to working as an independent contributor, Sai has worked as Assistant Manager – Cyber Risk Advisory for Deloitte, Team Lead – R&D for EC-Council, and Scientific Assistant – R&D for DLRL-DRDO, Ministry of India.
You can reach Sai at his LinkedIn profile: https://www.linkedin.com/in/praveenjalasutram/


