by Tom Pendergast, Chief Strategist of Security, Privacy and Compliance, MediaPRO
What was the first thing I did when the seriousness of the coronavirus pandemic hit me?
I didn’t go out and stock up on toilet paper, nor did I bathe my house in Purell (though I’ll admit, I sure wash my hands more now).
No, I went into a learning frenzy.
For several weeks, I couldn’t get enough detailed news and background about the virus and all things associated with it, and it couldn’t be sciency enough. The Johns Hopkins data site, interviews with Larry Brilliant, Tomas Pueyo’s essay “Coronavirus: The Hammer and the Dance” … WOW, I just sucked up whatever I could. (And look, I like Anthony Fauci, but the poor guy is fighting with one hand tied behind his back.)
The coronavirus turned me into a learning machine. I needed to deeply understand what was going on and how I should react.
I wasn’t alone; I know a bunch of people were trying to get smart on this stuff, fast. We were all motivated. As a culture, we needed to get smarter. And so here we are, staying home, staying safe.
And then, as soon as I felt that this learning mission was accomplished, my next thought was, how can we possibly replicate this for other circumstances? Specifically, how can I take what I’ve learned from this learning frenzy and put it to use in my goal to educate everyone—even my mother—on best practices for cybersecurity and privacy. So here are a few thoughts on how to do this:
#1: Take Advantage of a Crisis
First off, as crises go, the coronavirus, specifically the disease caused by it known as COVID-19, is a doozy. No one wants to deal with a crisis this big.
But let’s face it, small crises in cybersecurity and privacy come along all the time: on a global scale, we had the WannaCry malware, and on the local scale (meaning, your company), you may have a ransomware attack or a data breach or even something smaller and more benign. But the thing about a crisis is, it gets people’s attention—and it’s that attention that you don’t want to squander.
Crises create in many people a desire to learn more, to behave differently. They create motivations where there were none before. And let’s face it, they get attention. If you can leverage that attention and convert it into changed behavior, you’ll do a lot to accomplish your goals for increasing the acumen of your employees. But actually benefitting from a crisis requires more than just people paying attention; you’ve got to get them to focus on the right things.
I’m not suggesting that you become an ambulance chaser, trying to profit off a disaster. But cybercriminals have seized on this crisis to try to attach people and companies, and we owe it to our employees and families to teach them how they can keep from becoming victims during such crises.
#2: Communicate with Clarity
What are the top things you should do to protect yourself and your family from the coronavirus?
I’ll give you a second to come up with your top items, but I’d put good money on them including: wash your hands, cover your cough, and then (as the pandemic spread), stay home.
Very quickly, communications about the virus became hyper-focused on the few critical things that individuals could do to protect themselves, their families, and their communities. Over and over, those actions were expressed with utter clarity—and it’s that kind of clarity that we need to include in our cybersecurity communications.
I know that our company (and many others in our space) quickly communicated some simple things people could do to work safely at home: ensure your WiFi network was secure, connect via VPN or virtual desktop, update your software. It’s that level of clarity—tightly aligned with the crisis event that is capturing your audience’s attention—that is so critical.
#3: Communicate Visually
I’d read quite a bit about social distancing and why it helped slow the spread of disease, but it didn’t fully connect in my head until I saw the image. You know the one I’m talking about: X-Y axis, two curves, one level line of capacity. Once I saw that image—and it was suddenly everywhere—then it all made sense. Who didn’t want to flatten the curve?
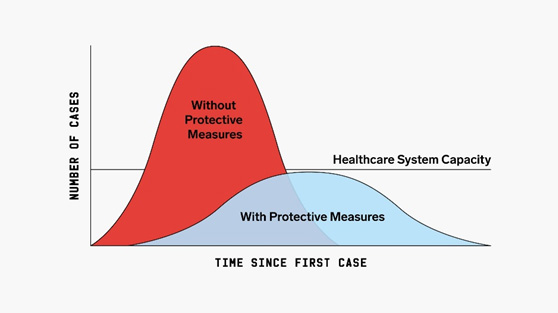
Now I know of no such clarifying visual for cybersecurity—no single image that would make the key objective crystal clear. But that doesn’t mean that we shouldn’t seek clarifying visual expressions behind the things that people can do to protect data in their environment.
Maybe it’s the icon on your phish reporting button that helps remind people to report phishing attempts. Maybe it’s the cool logo you’ve associated with your incident reporting process that makes it that much easier for people to report. Hell, maybe it’s the goofy character in your video about software updates that sticks in people’s heads.
Whatever the visual is, the point is that you shouldn’t miss the opportunity to visualize the problem and the solution that you’re trying to promote.
#4: Leverage Your Champions
No matter how big the crisis, people are by nature going to look to those they trust to help them make sense of the world seemingly falling down around them.
Look no further than our current crisis, when a little-known doctor with steady, reasonable advice—Anthony Fauci—quickly came to be one of the most trusted voices on the crisis, overshadowing the pronouncements of the U.S. President.
It wasn’t just that Dr. Fauci made more sense (though he did), but rather that he was a man who had been trusted by multiple presidents and who was trusted and respected by scientists around the world. He was a champion for a scientific approach to slowing the spread of the virus.
You have champions in your environment as well. They can be in any position—managers, the friendly IT guy who always has a moment, the one sales person obsessed with cyber—and they’re the people who are trusted by their peers to spread only reputable information. In a crisis, it’s important that you use those champions to spread your message, to leverage their own connections and authority to help ensure that people act on the things that help improve the security posture of the organization.
#5: Recognize that Behavior Change Takes Time
It’s been about a month and half since the coronavirus threat really took hold, and I think I’m just getting to the point where I don’t habitually touch my face.
Despite repetition after repetition from health experts all over the world, this particular habit has been extremely difficult to break (I just caught myself doing it now!).
The Washington Post ran a piece in early March touching on this exact point. The gist: we touch our faces to satisfy some need. Scratch an itch. Shoo away an insect. This satisfaction reinforces this behavior, leading us to do it more often.
We humans are habitual habit-formers; the Post article argues that it’s in our DNA. So it makes sense that changing a long-term habit is going to take a multi-pronged approach.
We can’t simply be told not to touch our faces. We need additional cues to make the behavior change stick. For me it was always keeping tissues in my line of sight . When I’d make the move to scratch my face, I’d see the tissues and be reminded I should take one out of the box and use it as a barrier between my bare finger and face to avoid skin-to-skin contact.
For training and awareness managers, my point is twofold.
One, give your learners some slack. Phishing emails work so well because opening an email and clicking on a link has become engrained in all of us. Every email is a little hit of dopamine, and changing that opening habit will take multiple cues to change. Don’t lose hope if some of your learners still struggle after only a second simulated phishing campaign.
Two, be prepared to deliver training and communications that work best for different learner types. The tissue solution worked for me but wouldn’t necessarily work for everyone. Have a toolbox of multiple ways of delivering education, be it online courses, short videos, email newsletters, or in-office events. Most importantly, be willing and able to repeat yourself.
#6: Keep a Sense of Humor
Look, this sucks. The deaths, the isolation, the uncertainty about the future … it’s hard. That’s why it feels so good to laugh every now and then.
Keep this in mind when you find yourselves issuing warnings about new phishing threats and reminders to turn on VPN. You don’t want to be negative nelly all the time. Every now and then you get to be the funny one.

In the End, It’s Not What the World Brings You, It’s How You React to It that Matters
There’s an old adage—I attribute it to the Stoics—that you can’t control what the world brings to your door, but you can control how you react to it.
We didn’t choose, and we certainly can’t control, the spread of COVID-19. But there’s encouraging news that we can both react to limit its destructive power and bring our communities together to reduce the misery that it causes.
The crises associated with cybersecurity are far different: they are not a sudden and dramatic onslaught, but rather a steady, persistent, and ever-shifting array of threats to information security. And while we can’t necessarily control the cybersecurity crises, we can react to them in ways that make our organizations more resilient and our communities more secure. Let’s do it together.
About the Author
Tom Pendergast is MediaPRO’s Chief Strategist of Security, Privacy and Compliance. He believes that every person cares about protecting data, they just don’t know it yet. That’s why he’s constantly trying to devise new and easy ways to help awareness program managers educate their employees. Whether it’s creating year-round programs to ensure employee commitment to cybersecurity and privacy best practices or working with teams of people to build and customize award-winning content, Tom is committed to getting employees, students, and even his mother to do the right thing when it comes to protecting data.
Tom holds a Ph.D. in American Studies from Purdue University, and has spent a career making complicated things simple, first as the founder of Full Circle Editorial, then in learning solutions with MediaPRO. For fun, he likes to scramble and trail run in the nearby mountains.
Tom can be reached online at @tompmediapro and at http://www.mediapro.com/


