by Jeremy Fuchs, Content Manager, Avanan
Recently, my phone was bombarded.
Just after the workday ended, I checked my personal Gmail account. Nothing was going on.
I rechecked it a few minutes later, and I had over 100 new emails. I checked it again a few minutes later—400 new emails. Then again, a few seconds later. 800 new emails. My first thought: Something has gone terribly wrong.
After a frantic Google search, I learned what had happened was a so-called “Email Bomb” attack.
Essentially, a bot was subscribing to my email address to tons of lists per second. It ran the gamut:

This newsletter looks nice—but alas, I don’t speak French.
This is a legitimate newsletter, but one I did not sign up for.
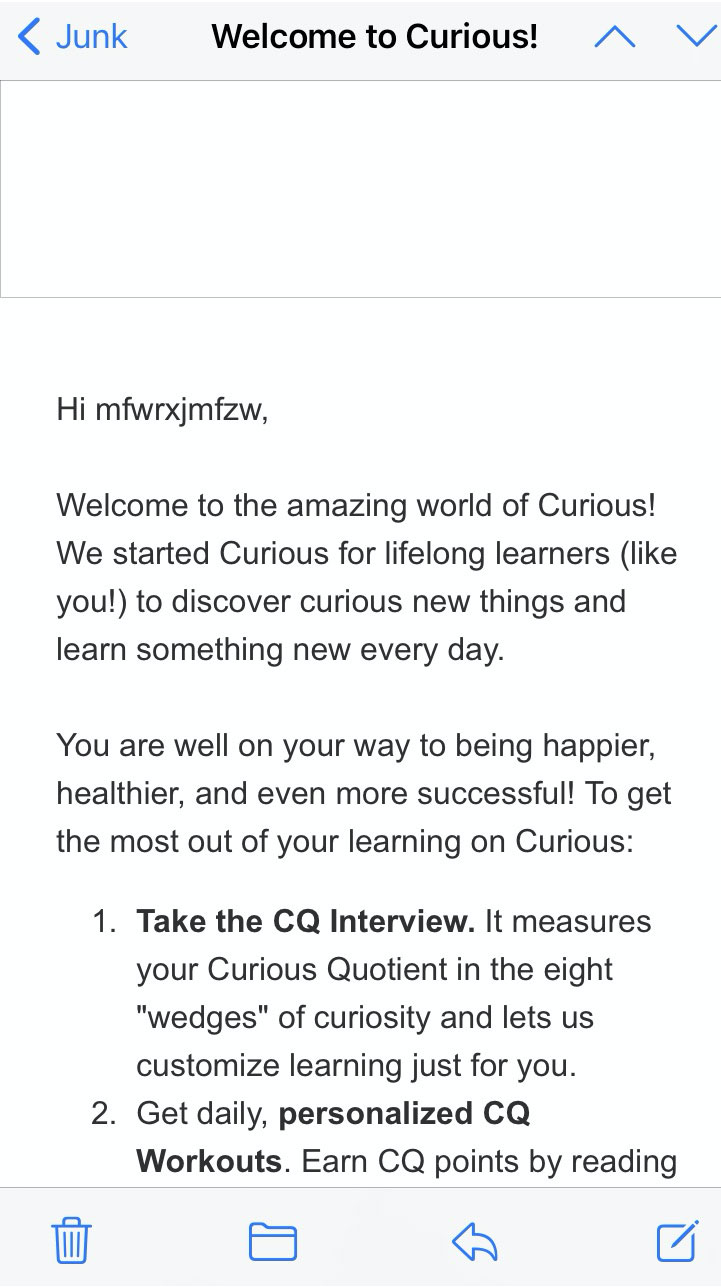
Notice the name that was filled in: mfwrxjmfzw. That’s a telltale sign that the bot was creating a script to sign up for tons of these newsletters at once. It wasn’t targeted—if it was, my name and other info would’ve been there. Instead, it was random letters, indicating a mass operation.
This was obviously disconcerting, especially since all of these emails were coming directly into my inbox at a rapid pace. Were any malicious? Were any of my passwords or accounts compromised?
I quickly sprung into action, marking all of these as spam and unsubscribing. I then updated my passwords across the board. This slowed down the deluge, as most new emails went directly into Junk. (Not that it’s helped my Junk folder, which continually gets hit.) Still, over the next few days, emails were trickling into the inbox, leading me into a familiar routine of bulk selecting and reporting as spam. Over a month later, the emails still reach my inbox on occasion.
This is not just a me problem. These cases are starting to increase in velocity, affecting individuals and organizations. Depending on the traffic level, it can severely limit server function, prevent email communications and lessen network performance. Depending on the scale, it can lead to a DDoS. It can also distract from other, malicious activity.
For an individual, it’s a nuisance. For organizations, it can be crippling. Imagine end-users trying to figure out what’s going on; overstretched SOC teams fighting to block email while it’s still monitoring other security events—it’s a strain if it’s happening to one employee. Imagine if it’s happening to your entire organization. That doesn’t take into account the fact that end-users may have been compromised or could end up clicking on malicious links. The security implications are staggering.
However, with proper protections, these bombardments don’t have to happen. A proper solution will natively pick up any inbound spam and flag it as such. Spam isn’t necessarily malicious, but it can be, and so anny email security solution needs to scan for malicious links within the email. Oftentimes, the “unsubscribe” link is just another way for impersonators or bad actors to get the end-user to click on the bait.
If an organization is to be email bombed, your email security has to block it before it gets out of hand. When it does, security admins will be able to use analytic features to gain even more insight. Further, if an individual is receiving an unusual amount of emails, then creating an anomaly alert that admins can see is incredibly useful.
Taken together, all these protections ensure that your end-users won’t have to be sent on a frantic search to figure out what’s going on and how to stop it.
Email bombs can be devastating. With proper protection, it doesn’t have to be.
About the Author
Jeremy Fuchs is the content manager for Avanan, the leading cloud email and collaboration solution. Jeremy can be reached online at (email: [email protected], twitter: @AvananSecurity, LinkedIn: https://www.linkedin.com/in/jeremy-fuchs1/) and at our company website www.avanan.com.


