by André Ferraz, Founder and CEO, Incognia
As our lives have become increasingly digital, the need to protect our online accounts and our digital identities is becoming a priority for everyone. The global pandemic has accelerated digital transformation not only for companies but also for individuals. For many users, their smartphone is now their main device, going far beyond just a means for communication. Whether ordering products or managing money, today’s mobile apps offer streamlined interfaces designed to meet the short attention span of the mobile user. That is, until the user hits the pain of authenticating and remembering a password. Authentication for the mobile user is vitally important, given the large number of phishing attacks and stolen credentials circulating on the Dark Web. However, until now, most mobile apps have applied web-based security solutions to their mobile channel resulting in a lot of unnecessary friction for the mobile user.
One of the most exciting recent developments on the smartphone is the emergence of mobile-native security solutions that enable frictionless login to mobile apps. Friction-free, meaning it requires no action by the user. This new development is called zero-factor authentication (0FA), i.e. no information or “factor” needs to be supplied by the user. The focus on authentication factors has grown over the past ten years with the increasing use of multi-factor authentication (MFA) methods as a vehicle for increased security. The idea of MFA is that requiring the user to supply multiple pieces or “factors” of information increases the likelihood that the user is legitimate. These authentication factors include information related to who the user is, what the user knows and what information the user has in their possession.
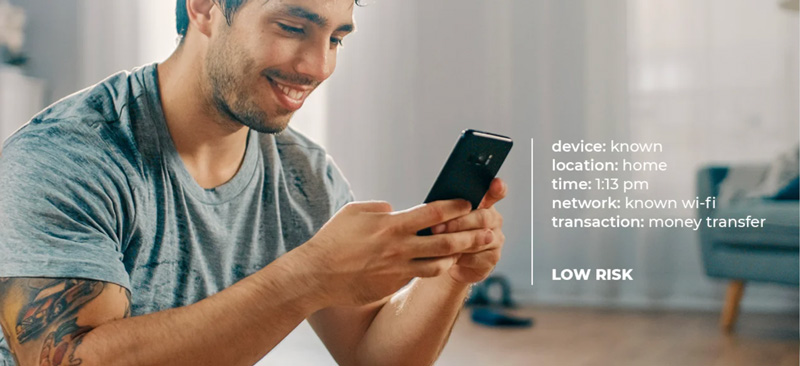
In zero-factor authentication, the user does not need to supply any information to authenticate at login or for sensitive transactions. Rather, the smartphone does the work. What makes this possible is the smartphone itself and its built-in technologies and sensors. Using signals from WiFi, GPS, cellular and Bluetooth networks, it is now possible to accurately identify a user based on their unique location behavior pattern like a location fingerprint. No two users have the same location behavior pattern and each user’s location behavior pattern is dynamic and constantly changing, making it extremely difficult to mimic or forge. If a fraudster attempts to login into a user’s account with stolen credentials, and the location pattern does not match, then login will be flagged as high-risk, requiring additional authentication steps in order to proceed. By using this 0FA method, the vast majority of legitimate users enjoy friction-free login, leaving additional authentication friction for the high-risk logins.
How does this zero-factor authentication work?
The main premise behind zero-factor authentication is that a legitimate user shouldn’t have to do all the work to prove they are legitimate. When a user opts in to allow use of location by an app, the app can use this information to build a unique location pattern that is used for frictionless authentication and fraud prevention.
What type of apps already use location?
The use of location makes it possible for apps to offer services such as locating the nearest store, or scheduling delivery to an address, or for ride sharing and transportation. In addition, location is now being used for zero-factor authentication to enable accurate fraud detection that is friction-free for legitimate users. For example, 75% of the top 50 finance apps already request permission to access location data.
How does a user know if location is being used for fraud detection?
Within a mobile app the user will see a pop-up screen asking permission to use location for fraud detection. This is the only action required of the user. At Incognia, we see greater than 85% of users opting in for fraud detection based on location, when the usage is clearly explained. However, the reality is that fraudsters will never share their true location, so they typically will not opt-in for location to be used. This means that location-based authentication is better used to protect legitimate customers than to detect and identify fraudsters.
What about location spoofing?
Legacy web-based security systems typically relied on GPS and IP for location. These location signals are easy to spoof and most fraudsters already have access to spoofing tools such as fake GPS Apps and mobile emulators. If location data is easily spoofed, it can’t be leveraged as a strong recognition signal. In addition, these technologies provide very poor precision for location e.g. an IP address might only pinpoint a location within a 10 mile radius, or GPS within a 100 foot radius. With this lack of precision it is not possible to uniquely differentiate users based on their location behavior, it would result in a large number of false positives i.e. legitimate users flagged as potentially fraudulent.
Advanced location technology that is being used for zero-factor authentication uses the combination of WiFi, GPS, cellular and Bluetooth signals to identify unique location environments and is able to pinpoint locations to within a 10 foot radius. Using this location precision, it is now possible to create a unique location behavior pattern for each user that can be used as a unique identifier.
What about privacy?
Users are becoming increasingly aware of the importance of ensuring the privacy of any data that they share. At Incognia we have a privacy-first design which places protection of user privacy as paramount. We believe users should be in control of their data, and that’s why zero-factor authentication is activated by the user. Users activate zero-factor authentication by opting-in for location sharing.
We believe the best way to keep personal information and location data separate, is to not collect any data that can directly link to identity. At Incognia we focus on encrypting and protecting the location data we collect with encryption and hashing techniques, and intentionally do not collect additional PII.
With zero-factor authentication now available on mobile, users can feel safe knowing not only that what they cannot see will not harm them, it is in fact protecting them against fraud.
About the Author
André Ferraz is the CEO and co-founder of Incognia. From Recife, a city in the Northeast of Brazil, where he studied Computer Science at the Federal University of Pernambuco. His entrepreneurial career, influenced by the academic work of his father, a researcher in Ubiquitous Computing, began when he was 19. His first company, Inloco, grew from a concept conceived in a university class into an award-winning location technology company that was recognized by the Institute of Electrical and Electronics Engineers (IEEE), the Association of Computing Machinery (ACM) and Microsoft as the world’s most precise geolocation platform. Today there are 60M+ devices leveraging Inloco’s technology.
Most recently, Andre founded Incognia, a private identity company that provides location-based behavioral biometrics to companies in consumer finance and mobile commerce for frictionless mobile identity verification and authentication. Built on the same privacy-first location platform Andre and his co-founders spent a decade developing, the company enables the use of anonymized location data to prevent new account and account takeover fraud. Incognia’s location technology uses network signals and on-device sensors to deliver highly precise location information without capturing any PII. By building an anonymous behavioral pattern, unique to each user, Incognia creates a private identity used to secure mobile accounts.
Incognia has teams in New York, Palo Alto and Brazil (where Inloco, was founded in 2014).


